YOUR TRUSTED PARTNER TO MEET YOUR CYBER SECURITY NEEDS
Specializing in cyber advisory, training, risk assessment, and virtual vCISO services.
Reducing risk through knowledge.
Cyber security threats are becoming more complex and the challenges to protect are becoming more difficult every day. Your organization needs to be risk aware.
You cannot protect what you do not know and to get the right solution in place, you need to understand your current threat position, what gaps exist in your current security posture, where to spend IT budget for the biggest impact, and what a risk resilient security approach should look like.
That is where RiskAware fits in.

What does RiskAware offer?
Managed Services
Designed for organizations with limited or no cyber security capability that need to respond to growing client and regulatory requests and of course the influx of cyber threats.
We provide everything you need to run a security program, from leadership to individual roles.
Professional & Project Services
Whether you are uplifting an existing cyber program or building a new one from scratch, we provide you with a team of experienced professionals.
We help you build effective security without adding to your team's workload.
Automation & Subscriptions
A little automation can go a long way. We offer subscription services to help your employees stay safe. Everything your team needs:
phishing simulation testing
dark web scanning
cyber training
We assist with cyber security guidance.
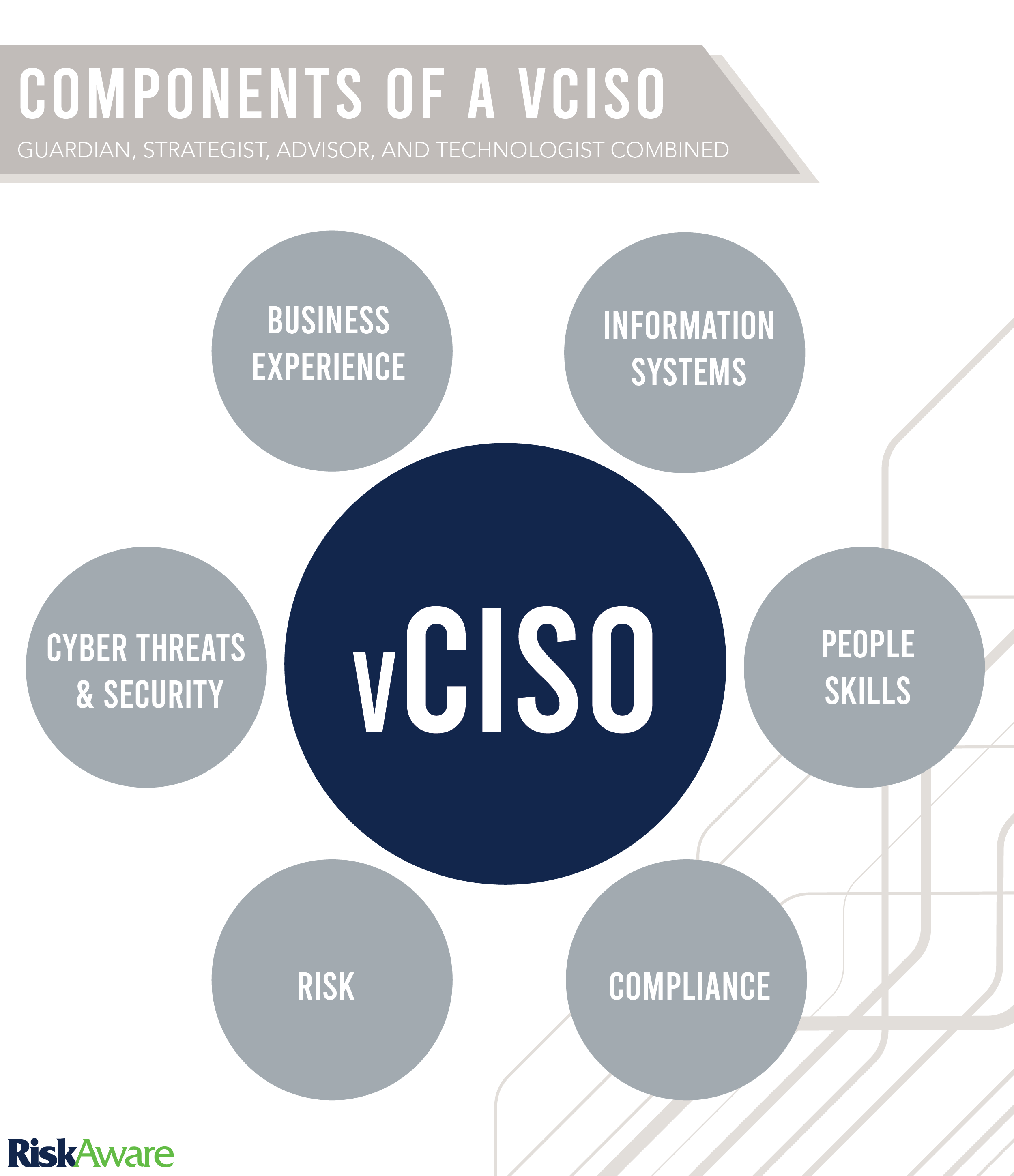
We bring a trusted and proven
cyber expert to your organization.
Our fractional CISO (vCISO) service is meant to give organizations with executive-level cyber security guidance to ensure cyber risk is properly managed.
Not all organizations require a full-time cyber security leader and the cost of paying for such (assuming you can find one) can easily exceed an organization’s operating budget.
Our on-demand virtual retainer model allocates a bucket of hours that can be allotted on capabilities as you see fit.
This allows organizations to gain instant cyber security expertise at a fraction of the total cost of hiring in-house security leadership.
Our clients can vouch for our work.
We are UpCity certified.
UpCity is a resource that helps connect businesses to service providers they can trust. With more than 50,000 listed providers—from marketing agencies to accounting firms to HR consultants, and many more—1.5 million businesses (and counting) have visited UpCity to identify the best partner for their needs. We are proud to partner with and be certified by UpCity.
Recognized as a leading innovator in our field.
We are experience driven and deliver results. We are a results oriented group of seasoned cyber experts. We ensure our clients have everything necessary to enable and grow their business.
Learn more about who we are and who we have worked with.









We look at cyber security from every point of view.
Regardless of the type of industry or size of your organization, we have identified key characteristics for a security program that we can adapt to meet your organizational demands:
Determine gaps and establish requirements
Measure against those gaps
Advise and educate
Execute on those changes

Latest Insights and Resources.
Journal.
The world is constantly changing and the challenges to cyber security are ever evolving.
Take a peek into the thought process behind the current events in our world. Written by our team of experts in the field.
News.
We are excited to share our strategic partnerships, scholarships, and press releases.
Keep up to date with the organizational changes in our community.
Downloads.
Our business resources are exactly the tools you need to understand your cyber security vulnerabilities and how we can help.
Explore our downloads for resources to accelerate change in your organization.
Press.
We are excited to share our press offerings with you.
Effective security is not complicated.
Protect what matters most to your organization, in a way that does not need to be confusing or unachievable.